Introduction to Modern Digital Payments
Evolution from Cash to Cashless Systems
Think about the last time you actually needed cash. Not wanted needed. Chances are, it’s becoming rare. Over the past two decades, the world has quietly shifted from physical currency to digital-first financial ecosystems, and this transformation didn’t just happen overnight. It’s the result of layered innovation, regulatory frameworks, and a deep integration of technology into banking infrastructure.
Initially, transactions were entirely dependent on physical presence cash exchanges, handwritten ledgers, and later, card swipes. Then came ATMs, which gave people 24/7 access to their money without stepping into a bank. That alone was revolutionary. But things didn’t stop there. With the rise of the internet, online banking and payment gateways began to emerge, allowing people to transact from their computers.
Fast forward to today, and we now have UPI (Unified Payments Interface) and mobile wallets enabling real-time, instant money transfers with just a few taps. According to recent data, India’s UPI system alone processes over 10 billion transactions monthly, a number that reflects how deeply embedded digital payments have become in everyday life.
But here’s the catch while these systems feel simple on the surface, what happens behind the scenes is incredibly complex. Multiple servers, encrypted channels, authentication layers, and banking networks are constantly communicating in milliseconds. It’s like a perfectly choreographed dance you never see.
Understanding this evolution isn’t just interesting it’s essential. Because once you see how these systems actually work, you start using them smarter, safer, and more confidently.
Why Understanding Payment Systems Matters Today
Let’s be honest most people use digital payments blindly. You tap “Pay,” see “Transaction Successful,” and move on. But have you ever wondered what actually happened in those 2–3 seconds? Where did your money go? Who verified it? And how did it reach the other person so quickly?
Understanding how digital payments work behind the scenes is no longer just for tech enthusiasts or bankers. It’s crucial for anyone who uses a smartphone which is practically everyone. Why? Because awareness directly impacts security, decision-making, and financial control.
For instance, knowing the difference between a payment gateway and a processor can help you identify safer checkout methods while shopping online. Understanding how UPI authentication works can protect you from common scams like “collect request fraud.” Even something as simple as recognizing how ATM networks communicate can make you more cautious about where and how you withdraw cash.
There’s also a bigger picture here. Governments and financial institutions are rapidly pushing toward cashless economies, aiming for transparency, efficiency, and reduced corruption. Countries like Sweden are already close to becoming fully cashless, and India is not far behind with its aggressive digital push.
From a user perspective, this shift means more convenience but also more responsibility. Cyber threats, phishing attacks, and digital fraud are evolving just as quickly as the technology itself. Being informed gives you an edge.
So instead of just being a passive user, think of yourself as an informed participant in a massive, invisible financial network. Once you understand the mechanics, you’ll start seeing every transaction not just as a tap but as a sophisticated process happening in real time.
How ATMs Work Behind the Scenes
Step-by-Step Process of an ATM Transaction
Card Authentication and PIN Verification
When you insert your card into an ATM, it might feel like a simple action but under the hood, a lot starts happening instantly. The machine reads the magnetic stripe or EMV chip on your card, extracting essential data like your card number, issuing bank, and expiration date. This data is not stored locally in the ATM it’s immediately prepared for secure transmission.
Next comes the PIN verification process, which is where things get serious. When you enter your PIN, the ATM doesn’t just “check” it locally. Instead, it encrypts your PIN using PIN encryption standards (like Triple DES or AES) and sends it through a secure banking network to your bank’s server.
Here’s the interesting part: your actual PIN is never stored in plain text anywhere. Banks store something called a hashed version of your PIN. So when you enter it, the system compares encrypted values rather than actual numbers. This makes it extremely difficult for attackers to retrieve your real PIN even if they intercept the data.
The ATM communicates with what’s known as an ATM switch, which acts like a traffic controller. It routes your request to the correct bank server whether it’s your bank or another bank in case of interbank transactions.
All of this occurs within just a few seconds. If the PIN matches, the bank sends back an authentication approval. If it doesn’t, the transaction is denied immediately.
What’s fascinating is how standardized and global this system is. Whether you’re withdrawing money in New York, Mumbai, or Tokyo, the underlying process remains largely the same secure, encrypted, and lightning fast.
Bank Server Communication and Approval
Once your PIN is verified, the ATM moves to the next critical stage: requesting authorization for your transaction. Let’s say you want to withdraw $100. The ATM sends a request through the network to your bank, asking a simple question: “Does this account have enough balance, and is this transaction allowed?”
This request travels through multiple layers ATM network → switch → interbank network (if applicable) → your bank’s core banking system. Each layer adds its own level of verification and logging.
Your bank then checks several things:
- Available balance
- Daily withdrawal limits
- Account status (active, frozen, etc.)
- Fraud detection flags
If everything checks out, the bank sends an approval message back through the same route. If not, it sends a denial with a reason code.
Once approval is received, the ATM’s internal system activates the cash dispenser module, which physically counts and dispenses the requested amount. Simultaneously, a receipt is generated, and your account balance is updated in real time.
All of this from card insertion to cash dispensing usually takes less than 10 seconds. It’s a perfect example of how hardware, software, and banking infrastructure work together seamlessly.
But here’s something most people don’t realize: the ATM itself doesn’t “decide” anything. It’s just a terminal. The real decision-making happens at the bank’s server level, miles away.
Role of ATM Networks and Switches
If ATMs were isolated machines, they’d be almost useless. What makes them powerful is their connection to a vast web of ATM networks and switching systems that act like invisible highways for financial data. When you use an ATM that doesn’t belong to your bank, it’s these networks that make the transaction possible.
At the center of this ecosystem is something called an ATM switch. Think of it like a highly intelligent traffic controller. The moment you initiate a transaction, the switch determines where your request needs to go. If you’re using your own bank’s ATM, the request is routed internally. But if it’s another bank’s ATM, the switch sends your request through an interbank network such as Visa, Mastercard, or regional networks like RuPay.
Here’s where it gets interesting: these networks don’t just route data—they also enforce rules. They ensure compliance with transaction limits, apply fees, and maintain logs for every single operation. So when you see a message like “You may be charged a fee,” that’s the network at work behind the scenes.
The speed is almost unbelievable. These switches can process thousands of transactions per second, ensuring that even during peak hours, your withdrawal or balance check goes through without noticeable delay. Behind the scenes, multiple redundant systems ensure uptime, meaning even if one server fails, another takes over instantly.
There’s also a settlement process involved. If you withdraw money from another bank’s ATM, your bank doesn’t immediately transfer the money. Instead, transactions are recorded and settled in batches later through clearing systems. This is why banks can keep operations efficient while still offering real-time user experiences.
Without ATM networks and switches, the convenience we take for granted like withdrawing cash from almost anywhere simply wouldn’t exist.
Security Mechanisms in ATM Transactions
Security in ATM transactions is not just important it’s absolutely critical. Every time you insert your card and enter your PIN, multiple layers of protection kick in simultaneously to ensure your money and data remain safe.
First, there’s encryption. All communication between the ATM and the bank’s server is encrypted using industry-grade protocols. This ensures that even if someone intercepts the data, they won’t be able to read or misuse it. Your PIN, in particular, is protected using Hardware Security Modules (HSMs), which are specialized devices designed to handle sensitive cryptographic operations.
Then comes physical security. Modern ATMs are equipped with anti-skimming devices that prevent fraudsters from attaching card-reading tools. Many machines also have tamper detection systems if someone tries to open the machine, it can shut down or alert authorities instantly.
Another fascinating layer is behavioural monitoring. Banks use AI-driven systems to analyze transaction patterns. If something unusual happens like a sudden large withdrawal in a different city the system can flag or even block the transaction in real time.
Let’s not forget two-factor authentication (2FA), which is becoming more common in ATM usage. Some banks now require OTP verification for large withdrawals, adding an extra layer of security beyond just the card and PIN.
Here’s a quick look at common ATM security features:
| Security Feature | Purpose |
| Encryption | Protects data during transmission |
| HSM (Hardware Security Module) | Secures PIN processing |
| Anti-skimming devices | Prevents card cloning |
| AI fraud detection | Identifies suspicious activity |
| OTP verification | Adds extra authentication |
Despite all these measures, user awareness still plays a huge role. Covering your PIN, avoiding suspicious machines, and monitoring your account regularly can make a significant difference.
Understanding UPI (Unified Payments Interface)
What Happens When You Send Money via UPI
UPI feels almost magical, doesn’t it? You enter a phone number or scan a QR code, hit “Pay,” and within seconds, the money lands in the recipient’s account. No bank details, no waiting period. But behind that simplicity lies a highly sophisticated system.
When you initiate a UPI payment, your app sends a request to the UPI network, managed by the National Payments Corporation of India (NPCI). The first step is identifying the recipient using a Virtual Payment Address (VPA something like name@bank. This eliminates the need for traditional bank details.
Next, your app securely sends the transaction request to your bank. You authenticate it using a UPI PIN, which works similarly to an ATM PIN but is specifically designed for digital transactions. Once authenticated, your bank forwards the request to NPCI, which then routes it to the recipient’s bank.
The recipient’s bank checks if the account is valid and able to receive funds. If everything checks out, the transaction is approved, and the money is instantly debited from your account and credited to the recipient’s account.
All of this happens in real time, usually within 2–5 seconds. That’s what makes UPI revolutionary it’s not just fast; it’s instantaneous settlement, unlike traditional systems that rely on batch processing.
Another key aspect is interoperability. You can use any UPI app Google Pay, PhonePe, Paytm—and still send money to anyone else, regardless of their app. That’s because the backend infrastructure is unified.
It’s a perfect blend of simplicity for users and complexity behind the scenes.
Request Initiation and VPA Mapping
At the heart of every UPI transaction lies something deceptively simple: the Virtual Payment Address (VPA). Instead of remembering long account numbers and IFSC codes, you just use an identifier like rahul@okaxis. But how does the system know where to send the money?
This is where VPA mapping comes into play. When you enter a VPA, the UPI system queries a central directory maintained by NPCI. This directory maps the VPA to the actual bank account details but crucially, these details are never exposed to the sender.
Think of it like sending an email. You don’t need to know where the recipient’s server is located you just type the address, and the system handles the routing. UPI works in a similar way.
When you initiate a payment:
- The app sends the VPA to the UPI network
- NPCI identifies the corresponding bank
- The request is routed securely to that bank
This process is incredibly fast and highly secure. It ensures that users can transact without worrying about sensitive financial information.
It also allows for flexibility. You can link multiple bank accounts to a single app or even have multiple VPAs for different purposes.
Real-Time Settlement Process
One of UPI’s biggest strengths is its real-time settlement capability. Unlike traditional banking systems that process transactions in batches (like NEFT or RTGS), UPI operates on an Immediate Payment Service (IMPS) backbone.
Here’s what that means in practice: the moment you approve a payment, the funds are transferred instantly no waiting, no delays. The sender’s account is debited, and the receiver’s account is credited almost simultaneously.
Behind the scenes, NPCI acts as the central switch, ensuring that both banks update their records in sync. This requires extremely high system reliability and uptime, which is why UPI infrastructure is designed with multiple redundancies.
The system also supports 24/7 operations, including weekends and holidays. That’s a major shift from traditional banking, where transactions often depend on working hours.
From a technical perspective, real-time settlement involves:
- Instant debit authorization
- Immediate credit confirmation
- Simultaneous ledger updates
This level of synchronization is what makes UPI one of the most advanced payment systems in the world today.
NPCI’s Role in UPI Infrastructure
Behind every successful UPI transaction sits an organization most users never think about the National Payments Corporation of India (NPCI). If UPI were a city, NPCI would be the urban planner, traffic controller, and law enforcer all rolled into one. It doesn’t hold your money, and it’s not your bank, but it ensures everything moves smoothly between banks.
NPCI operates the central switching system that connects all participating banks and payment apps. When you initiate a payment, your request flows through NPCI’s infrastructure, which verifies, routes, and confirms the transaction. It’s essentially the backbone that makes interoperability possible allowing a user on one app to send money to someone using a completely different app.
One of the most impressive things about NPCI is its ability to handle massive transaction volumes. UPI regularly processes billions of transactions per month, with peak loads reaching millions per hour. To support this, NPCI uses highly scalable cloud infrastructure, load balancing, and failover systems to ensure minimal downtime.
NPCI also sets the rules and standards for UPI transactions. This includes transaction limits, dispute resolution frameworks, and security protocols. Banks and payment apps must comply with these guidelines to remain part of the network.
Another key responsibility is settlement coordination. While transactions appear instant to users, NPCI ensures that interbank settlements are accurately recorded and reconciled. It acts as a neutral intermediary, ensuring trust between all participating entities.
Without NPCI, UPI wouldn’t just slow down it simply wouldn’t exist in its current seamless form. It’s the invisible engine powering one of the world’s most advanced digital payment ecosystems.
UPI Security Layers and Fraud Prevention
With great convenience comes great risk and UPI tackles this challenge with multiple layers of security and fraud prevention mechanisms. While the system is designed to be user-friendly, it’s anything but simple when it comes to safeguarding transactions.
The first line of defence is two-factor authentication (2FA). Every transaction requires something you have (your phone) and something you know (your UPI PIN). This ensures that even if someone gains access to your device, they still can’t complete a transaction without your PIN.
Then comes end-to-end encryption. All data transmitted between your app, bank, and NPCI is encrypted using advanced protocols. This prevents interception and ensures data integrity during transmission.
UPI also uses device binding, which links your account to a specific mobile device. If someone tries to access your account from another phone, additional verification steps are triggered. This significantly reduces unauthorized access.
Banks and apps also employ AI-based fraud detection systems. These systems analyze transaction patterns in real time. For example, if you suddenly send a large amount to an unknown account at an unusual hour, the system may flag or block the transaction.
Here’s a quick breakdown of UPI security layers:
| Security Layer | Function |
| UPI PIN | Authenticates user transactions |
| Device Binding | Links account to a specific device |
| Encryption | Secures data transmission |
| AI Monitoring | Detects suspicious behavior |
| Transaction Limits | Reduces risk exposure |
Despite these safeguards, many fraud cases occur due to user error, such as approving malicious “collect requests” or sharing OTPs. So while the system is secure, awareness remains your strongest defence.
How Digital Payment Gateways Work
Payment Gateway vs Payment Processor
When you pay for something online, two key players work behind the scenes: the payment gateway and the payment processor. They sound similar and many people use the terms interchangeably but they serve very different roles.
A payment gateway is like a digital bridge between you and the merchant. It captures your payment details card number, expiry date, CVV and securely transmits them to the payment processor. Think of it as the front-end interface that ensures your data is safely handed off.
The payment processor, on the other hand, is the engine that actually moves the money. It communicates with card networks (like Visa or Mastercard) and banks to authorize and complete the transaction.
Here’s a simple analogy: imagine you’re at a restaurant. The gateway is the waiter who takes your order, and the processor is the kitchen that prepares the food. Both are essential, but they do different jobs.
A quick comparison makes it clearer:
| Aspect | Payment Gateway | Payment Processor |
| Role | Captures & encrypts data | Processes transaction |
| Interaction | User-facing | Bank/network-facing |
| Function | Secure data transfer | Authorization & settlement |
Understanding this difference helps you appreciate how layered and secure online payments really are.
Step-by-Step Online Payment Flow
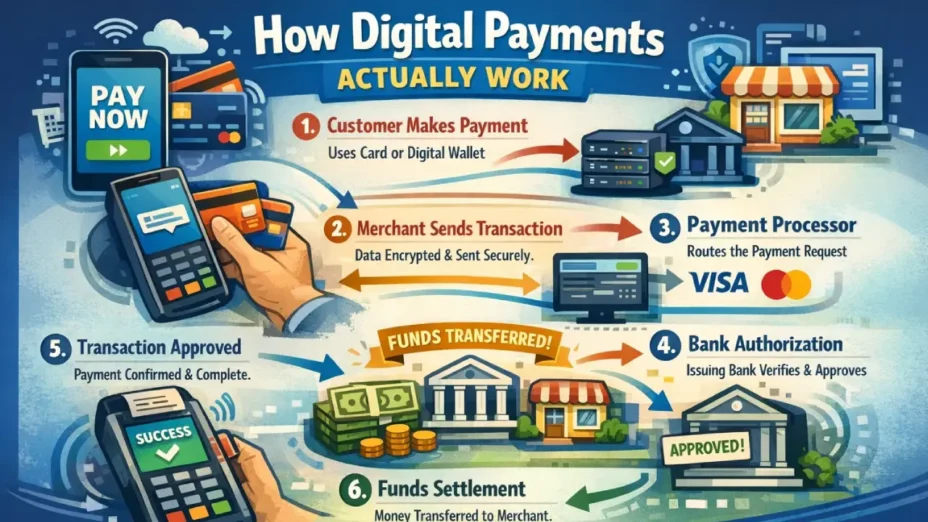
Let’s break down what actually happens when you click “Pay Now” on an e-commerce site. It may look instant, but behind the scenes, it’s a carefully orchestrated sequence of events.
First, you enter your payment details. The payment gateway encrypts this data and sends it to the payment processor. The processor then forwards the request to the card network, which routes it to your issuing bank.
Your bank checks several factors:
- Available balance or credit limit
- Card validity
- Fraud indicators
If everything looks good, the bank sends an authorization approval back through the same chain—bank → network → processor → gateway → merchant.
Once approved, the transaction is marked as successful. But the money doesn’t move immediately. Instead, it goes through a settlement process, where funds are transferred from your bank to the merchant’s bank, usually within 1–3 business days.
This entire process takes just a few seconds from the user’s perspective. It’s a perfect example of how multiple systems collaborate seamlessly to deliver a smooth experience.
Encryption and Tokenization Explained
Security is the backbone of digital payments, and two technologies play a major role here: encryption and tokenization. While they might sound technical, their purpose is simple keep your data safe.
Encryption transforms your sensitive data into unreadable code during transmission. Even if someone intercepts it, they won’t be able to decipher it without the encryption key.
Tokenization, on the other hand, replaces your actual card details with a randomly generated token. This token is useless outside the specific transaction, making it extremely secure.
For example, instead of storing your card number, a system might store something like X7A9-3F2K-L8P1. Even if hackers access this token, they can’t use it to make transactions elsewhere.
Together, these technologies ensure that your financial information remains protected at every stage.
Comparing ATM, UPI, and Digital Payments
Speed, Cost, and Convenience Comparison
When you look at ATMs, UPI, and digital payment gateways, each serves a different purpose but how do they stack up against each other? The answer depends on what you value most: speed, cost, or convenience.
UPI clearly leads in speed. Transactions are completed in real time, often within seconds, regardless of the time or day. Digital payments via gateways are also fast but may involve settlement delays. ATMs, while quick for cash withdrawal, don’t offer the same flexibility for transferring money.
In terms of cost, UPI is often free or extremely low-cost, making it highly accessible. ATM transactions may involve fees, especially for interbank usage. Payment gateways usually charge merchants a percentage per transaction, which can indirectly affect pricing.
Convenience is where digital systems shine. With UPI and online payments, you can transact from anywhere no need to visit a physical location. ATMs still play a crucial role, especially in cash-dependent scenarios, but they lack the flexibility of digital platforms.
Which System is Safer?
Safety isn’t about which system is “best” it’s about how well each system manages risk. ATMs rely heavily on physical and PIN-based security, while UPI and digital payments use multi-layered digital authentication.
UPI and online payments have the advantage of real-time monitoring and AI-based fraud detection, which can proactively prevent suspicious transactions. ATMs, while secure, are more vulnerable to physical threats like skimming.
That said, digital systems are more exposed to phishing and social engineering attacks, which makes user awareness critical.
The Future of Digital Transactions
AI, Blockchain, and Contactless Innovations
The next wave of digital payments is already taking shape, driven by AI, blockchain, and contactless technologies. AI is being used to enhance fraud detection, personalize user experiences, and even predict spending patterns.
Blockchain introduces the possibility of decentralized payments, reducing reliance on intermediaries. While still evolving, it has the potential to make transactions more transparent and secure.
Contactless payments—via NFC, wearables, and even biometric authentication—are making transactions faster and more seamless than ever.
What Users Should Expect Next
Looking ahead, users can expect:
- Faster and more secure transactions
- Greater integration with everyday devices
- Increased automation in financial management
The line between banking and technology will continue to blur, creating a more connected financial ecosystem.
Conclusion
ATMs, UPI, and digital payment systems may feel effortless, but behind every transaction lies a complex network of technologies working in perfect sync. From encrypted data flows to real-time settlement systems, these innovations have reshaped how money moves in the modern world. Understanding these systems doesn’t just satisfy curiosity—it empowers smarter, safer financial decisions in an increasingly digital age.
FAQs
1. Is UPI safer than using an ATM?
UPI is generally safer due to multi-layered authentication and real-time monitoring, but both systems are secure when used correctly.
2. Why do some ATM transactions take longer?
Delays can occur due to network congestion, interbank routing, or server verification processes.
3. Can UPI transactions be reversed?
UPI transactions are usually instant and irreversible, but disputes can be raised through banks.
4. What is the biggest risk in digital payments?
The biggest risk is user error, such as falling for phishing scams or sharing sensitive information.
5. How do payment gateways make money?
They charge merchants a small fee per transaction for processing payments securely.